1. Introduction
In this article you will find the most important topics relevant to an update of your Checkmk installation from version 2.4.0 to 2.5.0.
We recommend that you read through the entire article before updating so that you know exactly what to expect: before, during and after the update.
This article will be constantly revised during the beta period and after the release of Checkmk 2.5.0. If an important topic is missing, report an issue via GitHub. |
1.1. Update path
Updates from Checkmk must always be performed from the latest patch release of the source version, to the latest patch release of the target version. An update from 2.4.0p1 to 2.5.0p3 therefore follows this path:
2.4.0p1 2.4.0p29 2.5.0p3
Major versions cannot be skipped. If you want to update from 2.3.0 to 2.5.0, first perform an Update to version 2.4.0.
1.2. New edition names
Since 2.4.0p24, Checkmk has been using new names for its editions that better reflect their functionality. If you have installed a patch release from 2.4.0p24 onwards, you will already be familiar with the new names from the web interface. While Checkmk 2.4.0 uses the old edition abbreviation in package names, Checkmk 2.5.0 switches to the new names. For package names, this will result in the following changes:
crecommunityceeprocceultimatecmemanaged
If you have created installation scripts that use the old scheme for package names, you will need to convert these scripts to the new naming scheme.
2. Preparations
This chapter gives you an overview of the things you should take into consideration before you perform the update. Probably not every item will be relevant for you: For each topic, you can check the corresponding box for your own reference and immediately move on to the next topic.
2.1. Backup
As with any update to production software, you should check that your backups are up to date before performing the update of Checkmk.
Does this affect you? Yes.
What will you need to do? If you create your backups automatically via Setup > Maintenance > Backups, first check there that your backups are up to date and that the most recent backup jobs have completed without errors.
For more information, see the articles on Backups and on Backing up and restoring sites.
From the update to 2.3.0, changes are rolled back in the event of a failed update (Werk #16408).
An update can fail due to an unexpected internal error, but also due to user input during the update process, for example by selecting the menu option |
2.2. Checking the hardware utilization
Checkmk 2.5.0 requires slightly higher system resources than 2.4.0. Before updating, it is therefore advisable to find out how much free capacity the servers used for Checkmk have available.
Does this affect you? Yes, but the extent to which you are affected depends heavily on how you use Checkmk.
What will you need to do? Make sure that there is sufficient free capacity available. For information on the expected changes in the use of hardware resources, refer to the following table:
Processor load |
A slightly higher processor load is to be expected when using many active checks and some special agents. Other areas could be optimized as required, which in many cases leads to a reduction in the processor load. As a rule of thumb: If the CPU load is below the number of processor cores × 0.8 and the CPU utilization is below 70 %, no problems are to be expected. |
Memory usage |
The memory usage of Checkmk 2.5.0 is about slightly higher compared to 2.4.0. When using OpenTelemetry, add at least 8 GB additional RAM, since the metrics backend needs this for efficient operation. |
Disk space |
The hard disk space requirement increases, especially when using OpenTelemetry. The amount of additional disk space needed depends on the volume of incoming OpenTelemetry metrics. |
2.3. Changes to OpenTelemetry monitoring
Checkmk 2.5.0 is switching to a new metrics backend for storing and querying OpenTelemetry data.
Does this affect you? Yes, if you are already using OpenTelemetry data in monitoring with Checkmk 2.4.0.
What do you need to do? First, before updating, you need to allocate additional memory for the metrics backend. Since fewer conversions of OpenTelemetry data take place, the CPU requirements are lower than with Checkmk 2.4.0. The switch to the metrics backend means that you will need to recreate most of your configuration for OpenTelemetry monitoring. An overview is provided in Werk #19133, and the setup is explained in the article on OpenTelemetry monitoring.
2.4. Licensing of Checkmk Pro
In Checkmk 2.5.0, licensing is standardized for all commercial editions. For Checkmk Pro, this means that you can only perform an update if Checkmk Pro has already been licensed in Checkmk 2.4.0.
For an unlicensed Checkmk Pro, the pre-update check will fail with the following message:
Update aborted with Error: A valid and non-expired license is needed before updating
Does this affect you? This only affects users of Checkmk Pro. The other editions are not affected.
What do you need to do? In Checkmk 2.4.0, make sure that the license data has been entered and transferred to Checkmk GmbH/Inc. For instructions on how to do this, see the licensing article in the Checkmk 2.4.0 User Guide.
2.5. Linux distribution versions
In Checkmk version 2.5.0, some outdated distributions are no longer supported.
Does this affect you? This will affect you if any of the following Linux distributions—still supported in 2.4.0—is installed on your Checkmk server:
Debian 11
SLES 15 SP3 bis SP5
If you are currently using one of the Linux distribution versions listed above, this must first be updated. Before updating Checkmk, first perform an version upgrade of the Linux distribution. Make sure that the target version of the Linux distribution is supported by Checkmk 2.4.0 and 2.5.0. You can find out which Linux distribution versions Checkmk supports in the Update matrix for version 2.5.0 and on the download page after you have selected the Checkmk version and your Linux distribution.
2.6. Agent Updater for Linux without 32-bit support
Until now, the agent plug-in for automatic agent updates was available on Linux as a binary for the x86_64 (64-bit) and i586 (32-bit) platforms.
With Checkmk 2.5.0, 32-bit support is being discontinued (Werk #18925).
Does this affect you?
This affects you if you use the Agent Updater and if you deliver the Agent Updater as a binary for hosts running Linux on 32-bit i586.
Hosts for which the Agent updater (Linux, Windows, Solaris) rule was previously set to use 32bit packaged binary as the executable format, will be automatically switched to the Agent Updater Python script (executable format Python script).
For this script to function, Python 3.7 with the following modules must be available on the host:
cryptographyrequestspysocks
After configuring these dependencies, we recommend switching to the Python script while still on 2.4.0 and testing the update.
2.7. No support for Python 2 agent plug-ins (Linux/Unix)
Starting with 2.0.0, Checkmk switched to Python 3 as the default interpreter for agent plug-ins written in Python (Werk #12149). In 2.5.0, support for Python 2 is completely removed (Werk #16908).
Does this affect you? This will affect you if you are monitoring older hosts that do not yet have a Python 3 interpreter installed.
The simplest way to ensure that all agent plug-ins can also be used with Checkmk 2.5.0 is likely to be configuring a Python 3 runtime environment on all affected hosts. Test this under 2.4.0 to ensure a trouble-free update.
If it is not possible to configure a Python 3 runtime environment on the hosts, you can continue using the Checkmk 2.4.0 agent with Checkmk sites that have been updated to 2.5.0. In this case, however, you must disable automatic agent updates.
Note that agent plug-ins without a file extension are executed via the shebang. You can therefore at your own risk use a Checkmk 2.5.0 agent with older (Python 2) agent plug-ins — after changing the shebang (to the path to the Python 2 interpreter) and removing the file extension. If you choose this approach, you must prevent such a manually-installed agent plug-in from causing conflicts. To do this, you must disable the corresponding Agent Bakery rule.
2.8. Browser support
Checkmk 2.5.0 uses new JavaScript features that are not available in older browsers. Which browsers are supported in which versions can be found in the System requirements.
Does this affect you? You will usually have automatic updates to the latest browser version enabled on desktop systems.
What will you need to do? Check the browser version you are using and install a more recent browser if necessary. If you are using single board computers, smart TVs or digital signage solutions to display dashboards and you have no control over the system browser, test that any required dashboards are displayed correctly before updating. If necessary, contact the hardware manufacturer for updates.
2.9. Authentication by GET parameter
Up to Checkmk 2.2.0, every automation user could be logged in with a username and password passed via GET parameters. This option has been reduced as of Checkmk 2.3.0 and has been removed in version 2.5.0 (Werk #16223 and #17345).
Does this affect you? This change also primarily affects users who display dashboards using single board computers, smart TVs or digital signage solutions without a connected keyboard.
What will you need to do? Read the article on dashboards to learn how to enable sharing of individual dashboards in Checkmk starting with version 2.5.0. As an alternative to using the GUI, you can also generate tokens for sharing dashboards via the REST API (Werk #19334).
2.10. Uninstalling Python modules
Checkmk 2.5.0 updates Python to 3.13.9. This update affects modules installed on a Checkmk site. In many cases, post-installed modules are incompatible with Python 3.13.9. In the worst case, obsolete modules overwrite the functionality of the modules supplied by Checkmk.
Does this affect you? This will apply to you if Python modules have been installed later in your site. This may be the case, for example, if you have explicitly installed Python modules for special agents or agent-based check plug-ins that you have written yourself or obtained from the Exchange.
To find out if Python modules have been installed in your site, look for the dist-info and egg-info directories:
If the search result is not an empty list, you will need to take action.
Make a note of all installed modules and then uninstall them:
To learn how to handle uninstalled Python modules after the update, see below.
2.11. Stricter certificate validation in Python 3.13
Upgrading to Python 3.13.9 also enables stricter validation of certificate chains. Only certificate chains are accepted in which the root and intermediate certificate authorities (CAs) contain the key usage extension (Werk #19034).
This section also describes workarounds that may pose security risks, for example by exposing you to the risk of machine-in-the-middle attacks. We always recommend taking the secure route and aligning your CA infrastructure with current standards. |
Does this affect you? This only applies to you if you connect to endpoints using special agents or active checks whose server certificates use a non-compliant certificate chain. Typically, these are certificates issued using a custom CA infrastructure. Certificates from commercial CAs, from Let’s Encrypt, or created using step-ca are not affected.
You can examine suspicious certificates on the command line (OpenSSL 3 is required for this):
In this case, the certificate was not rejected.
For any other issue, openssl will display the reason for the rejection.
Before updating to Checkmk 2.5.0, the recommended approach is to replace certificates identified as affected with compliant ones.
If this is not possible, certificate verification can be disabled entirely for many of the special agents included with Checkmk (but be careful: this carries the risk of machine-in-the-middle attacks!). Alternatively, instead of trusting the root certificates, you can trust the server certificates directly, which is more secure but more complex to manage.
The detailed procedure for this is shown in Werk #19034.
2.12. Packaged (MKPs) and non-packaged local files
Local files allow you to customize and extend the functionality provided by Checkmk.
These files are located in the local part of the site directory structure, i.e. in ~/local and can be located in extension packages or simply 'lying around'.
Local files can cause problems during an update if they no longer match the new Checkmk version.
Does this affect you? Since it is not possible for Checkmk to fully ensure the compatibility of local adaptations during an update, you should check your Checkmk site before an update to see whether local files are used, which ones they are and how they are organized.
First, use mkp list to search for extension packages (MKPs) present in the site.
Also use mkp find to get an overview of unpackaged local files in your Checkmk site.
If the output for one or both of these commands is not empty, you will need to take action.
For the MKPs found with
mkp list, you will need to distinguish whether they are extensions you developed yourself, or are externally-sourced (e.g. third party) MKPs. You can usually easily test the extensions you have developed yourself and adapt them if necessary. For externally-sourced MKPs, you should research whether there are known problems with Checkmk 2.5.0 and whether newer versions are available. In cases where functionality previously provided by the MKP is now provided by Checkmk 2.5.0, deactivate the package before updating.If by using
mkp findyou have found local files: Combine the files that belong together into MKPs. This will make it easier to later deactivate these en bloc if incompatibilities are detected following the update. If file paths withpython3appear here, go back to Python modules.In the case of MKPs that require different versions for Checkmk 2.4.0 and 2.5.0, you should have installed both package versions with correct compatibility information in Checkmk before performing the update. If different versions of a package are available, Checkmk automatically activates the appropriate version during the update. As central sites with Checkmk 2.4.0 can hold packages for 2.5.0 and distribute these to remote sites, this feature also helps when updating in a distributed monitoring with central setup.
2.13. Cisco Meraki special agent: remove the MKP
The special agent for monitoring Cisco Meraki, previously available in the Checkmk Exchange as MKP, is included with Checkmk starting with 2.5.0 (Werk #19547).
Does this affect you?
This only affects you if you have installed the cisco-meraki MKP.
Uninstall the cisco-meraki MKP before updating to 2.5.0.
Remember to also uninstall any dependencies installed via pip or as an MKP (depending on the features used in the Meraki SDK).
After updating to 2.5.0, we recommend deleting and recreating monitoring rules for Cisco Meraki.
2.14. Programming interfaces
Checkmk 2.5.0 introduces versioned successors for internal application programming interfaces (APIs) that were previously defined on an ad-hoc basis (Werk #18600).
This affects cmk.inventory_ui, cmk.password_store, and cmk.server_side_programs.
Since we reserve the right to make changes, the APIs mentioned use v1_unstable as their version number.
We will strive not to make any incompatible changes until v1.
In addition, the directory structure of the Bakery API is being reorganized, though this rarely causes any problems.
The internal, ad-hoc defined programming interfaces will remain available, but we cannot guarantee compatibility.
Does this affect you? The topic of APIs affects you if you have extended the check plug-ins delivered with Checkmk with your own, self-written plug-ins and/or if you use plug-ins from other sources.
What do you need to do?
If you encounter issues with the old, ad-hoc internal APIs, we recommend migrating the affected plug-ins to the new v1_unstable APIs.
You can view the complete API documentation in any site under Help > Developer resources > Plug-in API references.
You can also find the same content at docs.checkmk.com/plugin-api.
2.15. Deprecations in the REST API
Starting with Checkmk 2.5.0, the REST API is versioned.
Checkmk 2.5.0 currently includes REST API version v1.
Does this affect you? This may affect you if, for example, you use the Checkmk REST API in your own scripts.
The REST API version 1.0, which was delivered up to Checkmk 2.4.0, is compatible with the new version v1.
We nevertheless recommend updating API paths in your scripts to reflect the new versioning.
Deprecated endpoints or parameters of the Checkmk REST API are marked in the API documentation with the ![]() symbol.
symbol.
What do you need to do?
Open the REST API documentation via Help > Developer resources > REST API.
Search the page in your browser for Deprecated, check whether you are using deprecated elements in your scripts, and replace these before updating.
The REST API documentation usually includes instructions on how to replace features that no longer exist in the new version.
It is possible that new major versions of the REST API will be released during the development cycle of Checkmk 2.5.0. Because Checkmk itself and the REST API are versioned separately, you have the option to decide for yourself when to migrate your scripts to a newer version of the REST API. Deprecations of REST API versions — which are announced well in advance via Werks — take effect only with the next major version of Checkmk.
2.16. Incompatible changes
As in every Checkmk version, there are also changes to the software in the current 2.5.0 version which may have repercussions on your Checkmk installation. In Checkmk these changes are organized and documented in what we refer to as our Werks. A so-called incompatible change requires that you make manual modifications in order to allow existing functions to continue to run as usual and/or to be able to use new functions.
Does this affect you? In general there will be incompatible changes that will also affect your Checkmk installation, it is however impossible to make a general statement covering all possible situations. In this article we have collected those issues that apply to all or most Checkmk installations. In any case there may be additional changes that are relevant to you, for example in checks that you use in your installation.
What will you need to do? Following every update—including patch versions—Checkmk will show you the number and content of incompatible changes and ask you to check and take note of them. Before performing the update is the right time to check for any changes from version 2.4.0 that may have an impact on the update.
Starting with Checkmk 2.3.0, such Werks are no longer carried over, because by default only the Werks from the target version are displayed in Checkmk (Werk #15292). However, since Checkmk 2.5.0, all unconfirmed, incompatible Werks from the source version are copied during the update, so that information about these Werks is not lost during the update (Werk #15365).
It is also a good idea to get an overview of the incompatible changes in version 2.5.0 before the update: Open the list of Werks on the Checkmk website. In the description of a Werk, you will find information on what you may need to do to make the change compatible.
After you have carried out the update, the number and content of the incompatible changes will be displayed in the Checkmk interface and you will be asked to check and take note of them. Links help you to check so that you can find out with just a few clicks whether you are using an affected component. If it is certain that a Werk has no impact or you have made the required changes, confirm the Werk with Acknowledge.
3. Update
3.1. Best practices when updating
In this section we describe the best practices that we follow even when updating large Checkmk environments. These are certainly not mandatory in every environment, but they can make the process of updating easier for you.
Updating the Checkmk version
As a prerequisite, before updating to version 2.5.0, version 2.4.0 must have been installed on the Checkmk site.
First, update Checkmk to the latest 2.4.0 patch version, and then update it to the latest 2.5.0 patch version. You can find the versions in the section above regarding the update path.
Perform a test run of the update
In large environments, where obviously even restoring a current backup of your Checkmk environment could take quite some time, it is recommended to perform a test with a cloned site before updating the production environment. For this purpose, you can, for example, restore the last regular backup of your site under a different name:
Alternatively you can also copy your site using omd cp.
For this, however, the site must be stopped for a short time:
Then, perform the update first on this new cloned site, for example to check the above mentioned local changes in the new environment.
Temporarily disable agent updates
If you are using the automatic agent updates in the commercial editions, you should consider disabling them temporarily before updating Checkmk so as to be able to later switch to the new agents at the hosts in a controlled manner.
To do this, first select Setup > Agents > Windows, Linux, Solaris, AIX and on the following page select the menu item Agents > Automatic updates.
By clicking on the
![]() button in front of the Master switch you can disable the agent update completely:
button in front of the Master switch you can disable the agent update completely:
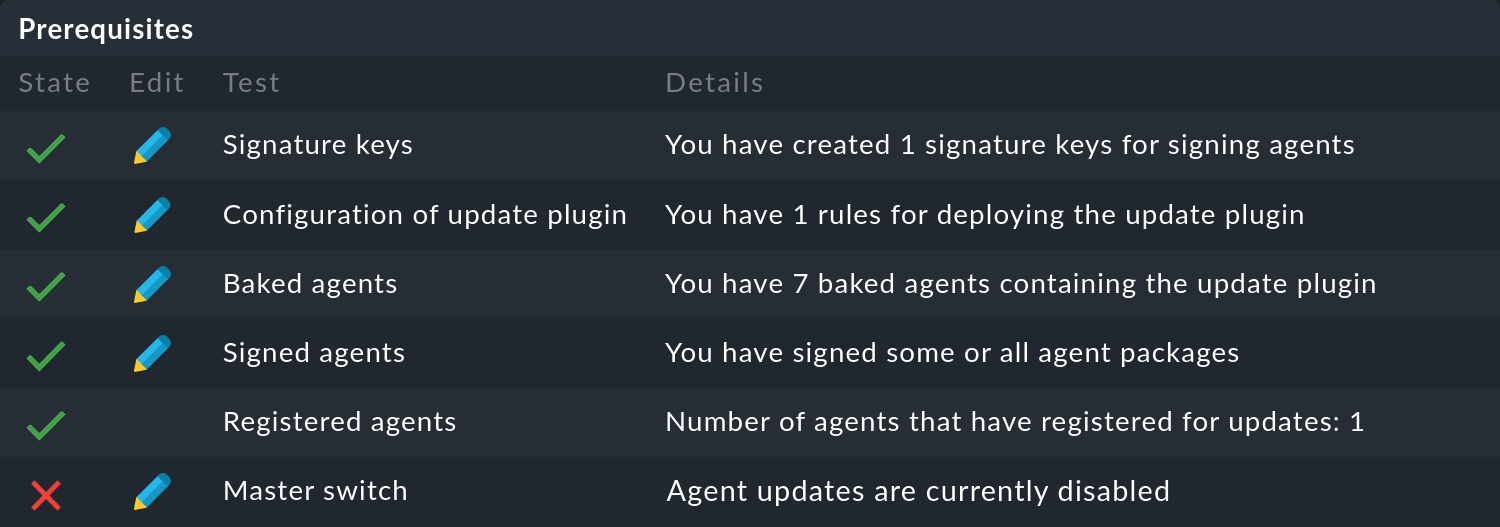
Following a successful update of Checkmk, you can reactivate the agent updates in the same way.
At this point, we recommend that you initially only reactivate the automatic agent updates for individual hosts or host groups. By doing so, the new agent will not be rolled out to all of your servers right away and you can familiarize yourself with the newly delivered data on a few systems. Also, due to the significant increase in the number of check plug-ins supplied, you might find a whole new set of services that you can then set up properly on the test systems of your choice. You may also need to define new thresholds for new services. If you tackle this on a small scale first, you will be able to minimize unnecessary false positives.
On the Automatic agent updates page above, you can simply enter a few hosts or host groups in the corresponding fields and then re-enable the Master switch.
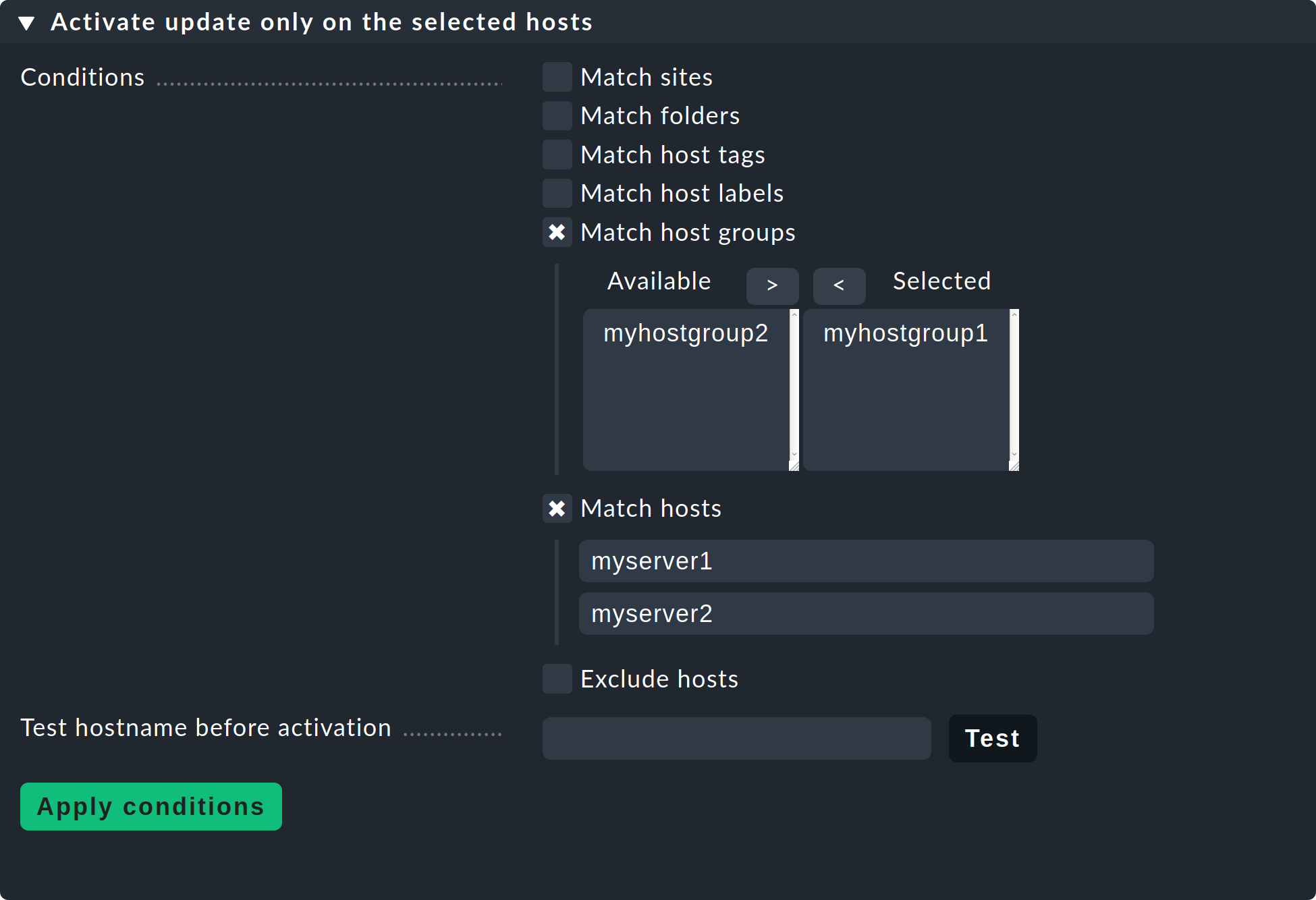
Remember to remove these restrictions on explicit hosts and host groups again once you are satisfied with the results. |
Temporarily disable notifications
You should also consider turning off notifications in the site before the update—for similar reasons to those we explained in the previous section on automatic agent updates. This way you avoid your colleagues from the monitoring team receiving unnecessary notifications.
You can turn off notifications centrally with the main Notifications switch in the Master control snap-in.
It may happen that after the update one or another service is CRIT, which had not been the case previously. Take care of new problems after the update for example, in the Overview snap-in.
Do not forget to turn on the notifications again, e.g. when following the update the number of unhandled problems has leveled off to the level seen before the update. |
Adjust the automatic service discovery
With each new version of Checkmk, some services are removed and new ones are added. To get an overview of these changes, you should review the settings for the discovery check and adjust them as needed. We recommend at least disabling the automatic deletion of services that no longer exist. Disabling the automatic addition of new services also helps you specify more precisely, in the phase following the update, which settings you want to use for discovery of the new services.
3.2. Updates in distributed monitoring
There are two different procedures for performing an update of all sites included in a distributed monitoring:
Stop all sites, perform the update of all sites in a bulk action, and then restart all sites.
Under strict conditions, a mixed operation is possible for a certain period of time, in which the remote sites are updated first, following which version equivalency is restored with the update of the central site.
In particular, if you want to update while the system is running, you should read the notes in the general article on Updates and Upgrades.
3.3. Performing the update
Nothing fundamental has changed with the actual update of the software in Checkmk 2.5.0, i.e. you install the new version, perform the update of the Checkmk site, rectify any possible conflicts and check and confirm the incompatible changes.
Perform the update procedure as described in the article on Updates and Upgrades.
Re-login required
The update from 2.4.0 to 2.5.0 introduces new environment variables that are required by some of the programs included with Checkmk.
If you performed the update in an interactive shell as a site user, exit this shell using the keyboard shortcut Ctrl+D.
If necessary, switch back to a shell as a site user using omd su mysite.
The new environment variables will now be available.
Repeat this procedure for all shells that were open during the update.
4. Follow-ups
4.1. Changes to the user interface
The user interface (GUI) in Checkmk has undergone a major overhaul in 2.5.0. For example, newly-created sites now have a welcome page, the search has been redesigned, activating changes is possible without leaving the currently open page, and more assistants are available, for example to quickly add the first hosts to a monitoring. Nevertheless, you can still use the general workflows you are familiar with from the 2.4.0 version in 2.5.0 with only a moderate learning curve.
We will present these changes in this User Guide’s articles—and in the Beginner’s Guide you will find a detailed introduction, including the most important elements of the user interface.
4.2. Updating services
As with every major version, Checkmk 2.5.0 introduces a whole new set of check plug-ins. If you do not use the 'discovery check', i.e. the automatic update of the service configuration via the periodic service discovery, you will have to search for services on quite a number of hosts.
If your hosts are organized accordingly (e.g. in folders), you can generally use the Bulk discovery function for this. This function can be found under Setup > Hosts > Hosts and then in the Hosts > Run bulk service discovery menu.
Service names
Each update of Checkmk will involve changing service names to improve the consistency of naming within the monitoring and documentation of Checkmk. Since changing service names means that rules sometimes need to be modified and historical monitoring data can be lost, Checkmk initially leaves the old names in place during an update. For services where the loss of old monitoring data is acceptable and the effort for adapting rules is manageable, you should switch to new service names as soon as possible.
To do this, go to Setup > General > Global settings > Execution of checks and go through the list Use new service names and identify the services where the checkboxes are not yet active and activate them. After applying the changes, the new service names will be active and a few minutes will pass before you see the defined states of the affected services in the monitoring again.
4.3. Vanished services
In some cases, check plug-ins had to be moved out, or check plug-ins had to switch to new APIs.
Does this affect you? The risk of being affected is present if you monitor hardware with a very long lifecycle, especially using special agents.
What will you need to do? If services disappear following the update, search the Werks for the manufacturer of the monitored products. In most cases, you will have to switch to new APIs or, in rare cases, use packages from the Exchange to monitor a specific hardware or software component.
4.4. Installing Python modules
Does this affect you? This will only apply to you if you have explicitly installed Python modules for special agents or agent-based check plug-ins that you have written yourself or obtained from the Exchange and have removed these in the course of preparing for the update.
First find out whether the previously uninstalled modules have already been delivered with the new Checkmk version, for example:
If the module has already been found, mark it as not required in your notes. Install the latest version of any modules that are not included:
Then test the check plug-ins or special agents that rely on Python modules installed in the site.
4.5. Agent Controller for Linux/aarch64
Until now, the Agent Controller for Linux was only available for the x86_64 platform; in Checkmk 2.5.0, aarch64 is being added.
Does this affect you?
If you have hosts in monitoring that run Linux on 64-bit ARM (aarch64), you previously had to transmit the agent output unencrypted or set up an SSH tunnel.
Since Checkmk 2.5.0 makes the Agent Controller available for both x86_64 and aarch64, it is no longer necessary to treat Linux hosts differently for the two platforms.
If you use agent packages with default settings, starting with Checkmk 2.5.0p1, you have the choice between two different agent packages:
A package for all architectures, which installs the Agent Controller on
x86_64and configures the agent in legacy mode everywhere elseAnother package that can only be installed on
aarch64(64-bit ARM) and installs the Agent Controller there
If you build agent packages using the Agent Bakery, you can use the Customize agent package (Linux) rule to specify in which agent packages you want to include the Agent Controller and for which platform.
Note that the Agent Updater, packaged as a binary, is currently limited to x86_64.
If you want to provide automatic agent updates to Linux hosts on aarch64, you must continue to deliver the Agent Updater as a Python script.
4.6. No agent plug-ins in VBS included (Windows)
As of version 2.5.0, VBS agent plug-ins provided by Checkmk for the Windows agent are a thing of the past. All included plug-ins have been ported to PowerShell (Werk #17685, #17686, #17687, #17688, #17689, #18111 and #18112). The minimum supported PowerShell version is 5.0. This means the new plug-ins are compatible with all Windows versions officially supported by the Checkmk agent.
Does this affect you? This affects you if you use Windows agents with agent plug-ins that were previously delivered as VBS. Plug-ins you wrote yourself or obtained from other sources, such as the Checkmk Exchange, will not be affected.
If you deploy agent plug-ins via the Agent Bakery, you do not need to do anything: Existing VBS plug-ins are now deployed as PowerShell plug-ins using the same Bakery rules.
If you distribute agent plugs-ins in other ways, you must ensure that you distribute the PowerShell plugs-ins in the future and delete the VBS plugs-ins.
If you encounter any issues with the new PowerShell plug-ins we have delivered, you can temporarily install the old VBS plug-ins from Checkmk 2.4.0 manually and continue using them. If we become aware of any problems, we will resolve them as quickly as possible and modify the behavior to match that of the old VBS plug-ins.
4.7. Paths for the FreeBSD agent
Previous FreeBSD agents used default paths that followed Linux conventions rather than FreeBSD conventions.
Does this affect you? This affects you if you have hosts in your monitoring environment that run FreeBSD or a system based on it (such as various firewall or storage solutions).
Immediately after updating the agent script to 2.5.0, you must move the configuration files from /etc/check_mk to /usr/local/etc/check_mk.
Variable data is now expected under /var/db/check_mk_agent (previously /var/lib/check_mk_agent).
Details can be found in Werk #18924.
4.8. Converting inventory trees
Checkmk 2.5.0 changes the storage format for inventory trees to JSON. Converting the inventory trees may result in performance gains (Werk #18032, #18033 and #18034).
Does this affect you? This will only affect you if you work extensively with the HW/SW inventory.
The conversion of inventory trees will be handled by a cron job every day at midnight following the update.
Since it may take a while for all inventory trees to be converted, we recommend running the command cmk-transform-inventory-files immediately after the update, at least for frequently-used trees (Werk #18033).
This will make the results of the manually converted trees available immediately.
4.9. Smart Ping supports IPv6
Currently, the status of hosts that are accessible exclusively via IPv6 is determined using the active check check_icmp.
This active check provides metrics such as round-trip times and packet loss.
Starting with Checkmk 2.5.0, Checkmk Micro Core (CMC) users can also use Smart Ping for these hosts (Werk #18050), although Smart Ping does not provide any metrics.
Does this affect you?
Hosts without an explicit configuration of the active check check_icmp will be automatically switched over.
As a result, the active check and its metrics will be removed.
If this is the desired behavior, you simply need to accept the changes to the service list.
Only if you do not want to do without the metrics of the active check for these hosts, a small manual configuration change will be necessary.
What do you need to do?
Adapt the configuration of the service discovery or the active check check_icmp.
You can find the description and the rules to be changed in Werk #18050.
5. The outlook
This chapter covers topics not directly related to the current Checkmk version 2.5.0, rather to future versions in development.
5.1. Microsoft SQL Server rule set (for Windows) will be removed
Checkmk 2.5.0 is the last version that supports rules for the old Microsoft SQL Server (Windows) plug-in. This will be removed in the next Checkmk version. Migrate to the new plug-in and the corresponding Bakery rules Microsoft SQL Server (Linux, Windows) in a timely manner. For more information, see Werk #17669.
5.2. The Prometheus scrape targets in the Prometheus rule set will be removed
The existing Prometheus Scrape Targets option in the Prometheus rule will be removed. For Kubernetes monitoring, switch to the Kubernetes special agent, and for generic Prometheus scraping endpoints, switch to the OpenTelemetry monitoring. Details are explained in Werk #18709.
5.3. Azure special agent v1 will be removed
The existing special agent for monitoring Azure will be replaced by version 2 in the medium term. In Checkmk 2.5.0, you will still be able to create new rules for the existing agent, but this option will be removed in the following Checkmk version. The dashboard for the existing Azure monitoring will also be less prominent in the menu. Read Werk #19467 and Werk #19282 to learn more.
5.4. The active check Check State of BI Aggregation will be removed
Until now, there have been two ways to monitor the status of BI aggregations: an active check and a special agent. The active check will no longer be included in the next Checkmk version (Werk #19340). Migrate to the BI aggregations special agent at the appropriate time.
5.5. The old HTTP check will be removed
Since 2.3.0 Checkmk already contains a new active check for HTTP connections and certificates. The Check HTTP web service can be found under Setup > Services > HTTP, TCP, Email, … in the Networking box. The new check is significantly better performing, more robust and easier to configure than the previous Check HTTP service. In addition, it is now possible to simultaneously monitor multiple things using a single rule, for example HTTP response codes, response times and certificate validity.
In Checkmk 2.4.0 some rarely-used options within the old check have been added to the new check to make migration easier. Furthermore, we provide a migration script that maps existing calls and resulting services 1:1. With Checkmk 2.5.0, you can no longer configure new rules for the old check. It will be completely removed later. Then the migration script will also no longer be shipped (Werk #19702). Therefore, perform the migration in Checkmk 2.5.0.
Once the migration has been completed, you can achieve significant performance benefits by merging multiple rules, allowing a single execution of the check to produce multiple outputs, thus reducing CPU overhead. In many cases you can also generate multiple services using a single rule in the new check.
General information on the new check can be found in the two Werks #15514 and #15515. Werk #17725 describes the migration script. A detailed blog article explains the details of the possibilities, limitations and best practices for preparing and following up the migration.
If you come across applications in which the new check cannot replace the old one, you can display the command line used in the same way as in the procedure described here.
You will then have the option of calling the old check, or a system-wide installed check_http via Setup > Other services > Integrate Nagios plugins.
5.6. Management boards
The term management board stands for separate plug-in cards or extended BIOS functionality (Baseboard Management Controller/BMC, Management Engine/ME, Lights Out Management/LOM) for monitoring and managing the hardware in addition to the installed operating system.
Up to Checkmk 2.4.0, management boards can be configured in two ways: As a host property or as a separate host. As the configurability as a host property is very limited, in the future this option will no longer be available.
Since Checkmk 2.4.0, Redfish monitoring is an integral part of the software (Werk #17404). We explain additional background information and possible alternatives in the Monitoring management boards blog article.
